Protopia AI is at RSAC. Meet our team of experts in AI Data Privacy and Security.
Protopia AI is at RSAC. Meet our team of experts in AI Data Privacy and Security.
Protopia AI’s Stained Glass Transform™ (SGT) expands the usability of sensitive data for AI and GPU optionality with state-of-the-art data protection and privacy.
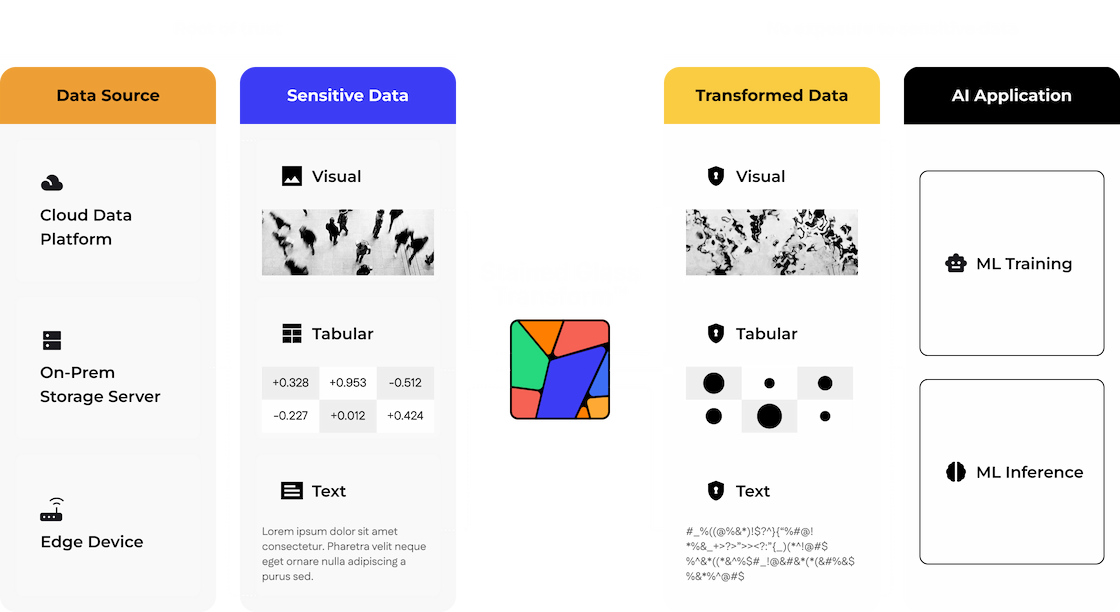
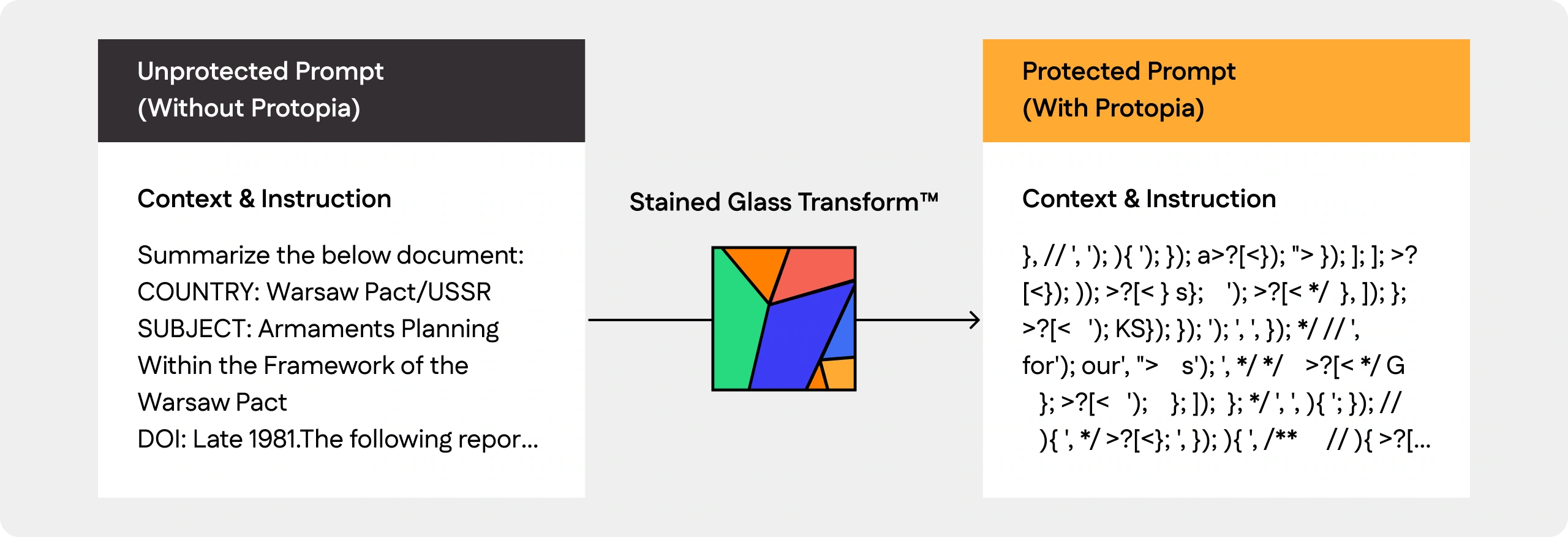
Stained Glass takes data from your root of trust and transforms unprotected data into stochastic representations that retain the data’s utility for target AI models while rendering it unintelligible to humans and to other AI models.
SGT holistically transforms the entirety of each data record using our patented technology into randomized representations that preserve the data’s functionality for target AI models.
The transformations are usable only by the target model, work across data modalities, and are non-deterministic, irreversible and computationally lightweight.
Stochastic representations of text for a language model holistically changes data for a customer classification task. The accuracy of the fine‑tuned LLM stays virtually intact.
Stained glass generates stochastic representations that enable VIP recognition task to operate accurately without exposing scene in unprotected & human recognizable format.
Protect your sensitive data at LLM inference endpoints with stochastic transformations that preserve utility for target models while remaining unintelligible to humans and other AI systems.
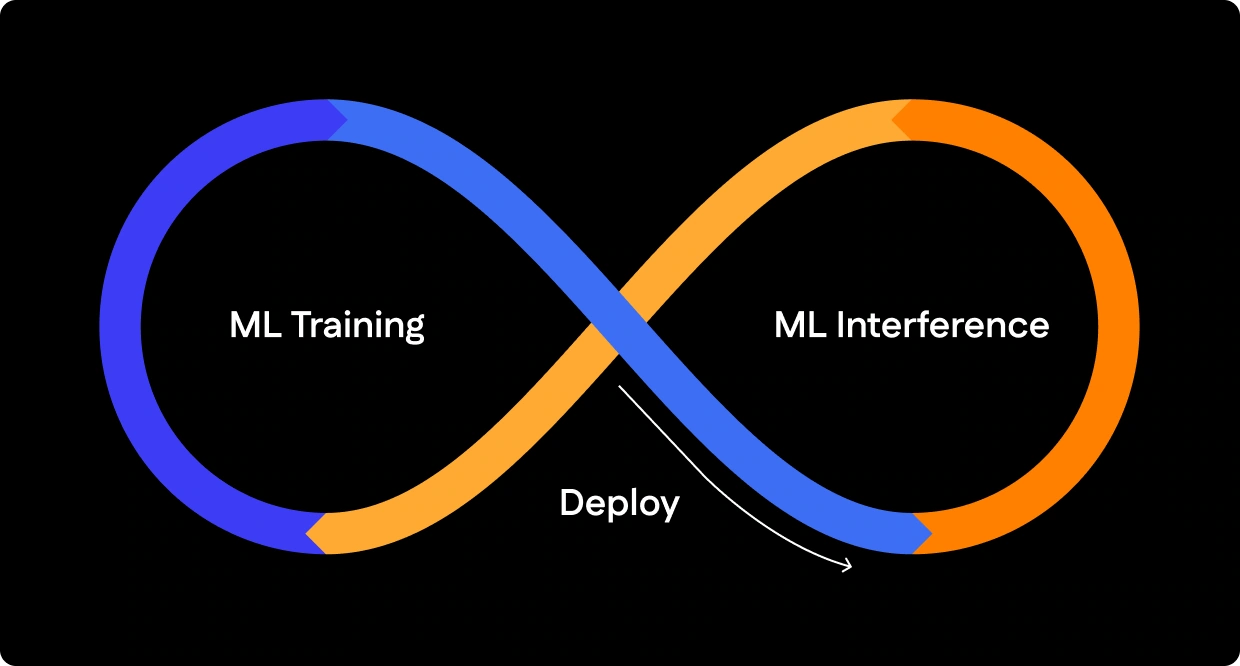
Data ownership and enterprise data confidentiality is not just for ML training. Enterprise data for AI-driven insights is just as confidential. Stained Glass protects data both during ML training and ML deployment.